The threats – real and perceived
[First posted 10 September 2020]
[minor changes 21 June 2021]
[Revised 24 May 2023]
[MINor changes 25 January 2025 – links checked]
Luckily, there’s plenty of advice and guidance available – often slanted particularly towards our demographic (ie oldies) …
Terrified -> Apprehensive -> Sensibly Aware -> Relaxed -> Unconcerned
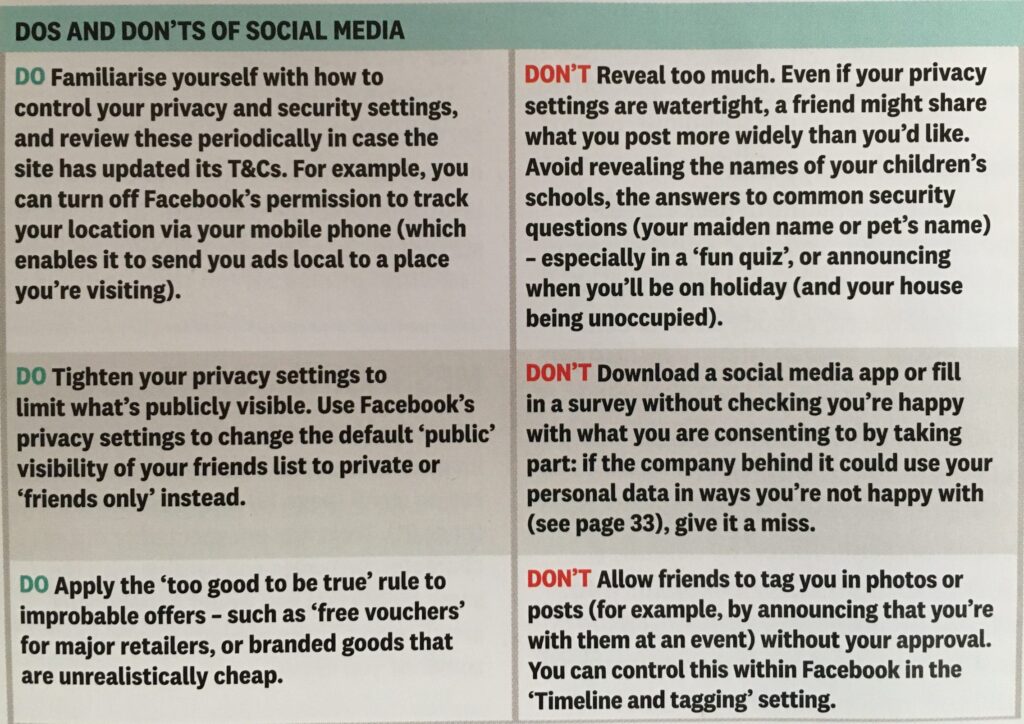
First let’s distinguish the difference between online security and online privacy. These are two different issues which are however linked. Sometimes you have to relinquish some privacy to receive a service – unless you choose to pay for it (and I’ve long been an advocate of paying for services if they do a job that is necessary); exactly how much privacy are you prepared to relinquish? Security on the other hand is an absolute – you should not be prepared to accept less than your very best efforts . We’ll deal with that in the third part of the post.How do you relinquish your privacy, and how much of a loss of privacy is acceptable?
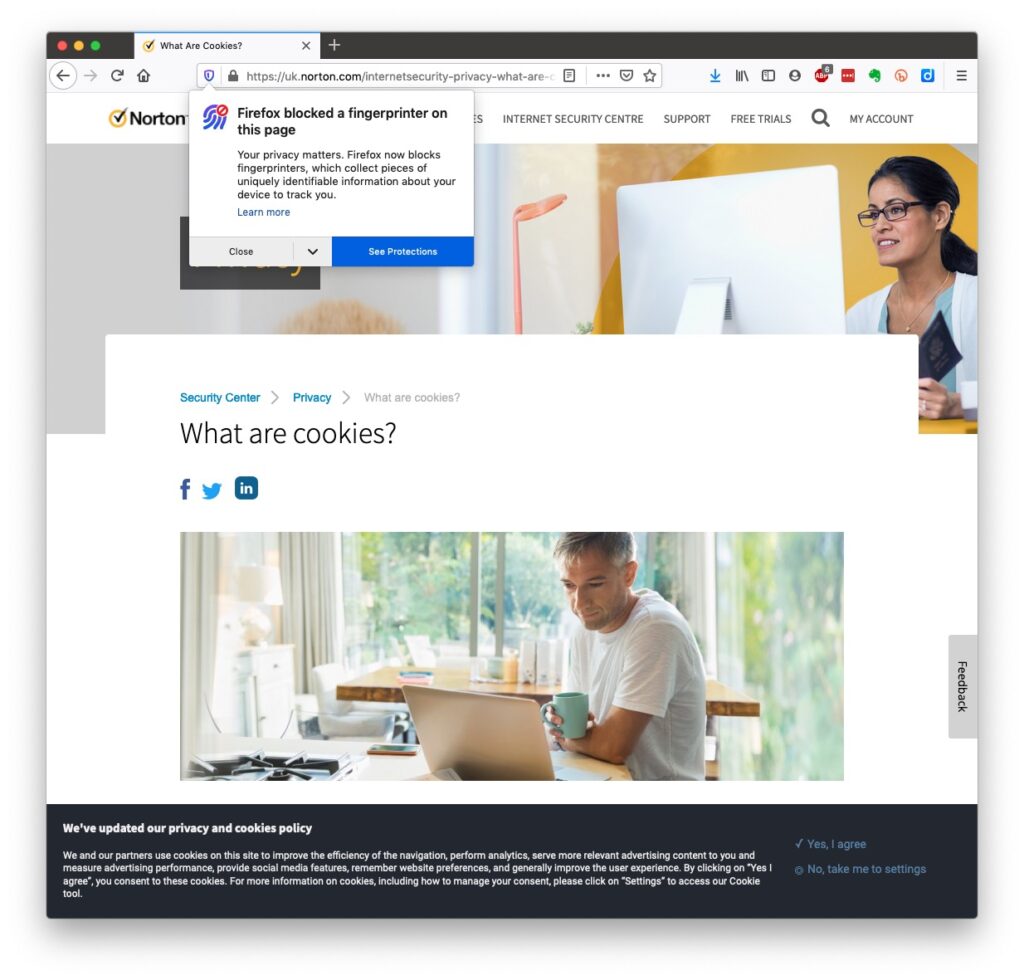
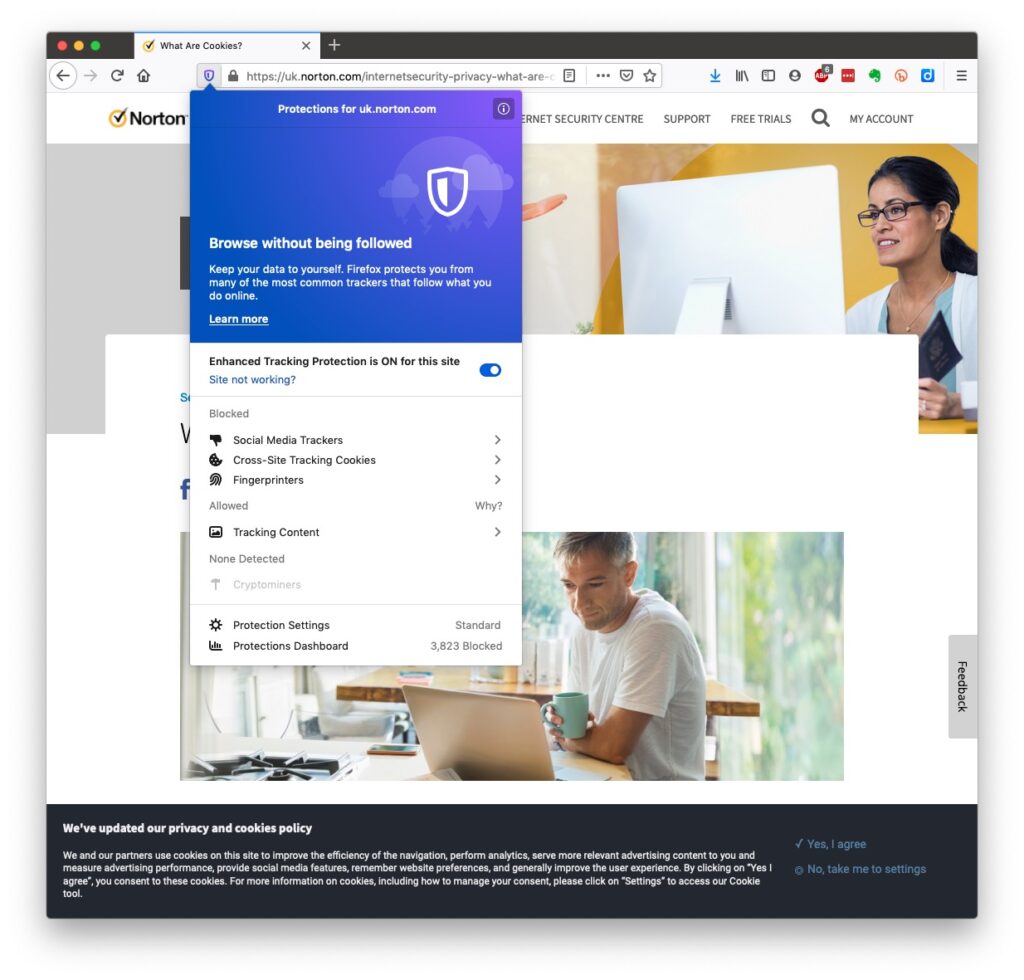
Some services could not be offered without income from adverts, or paid-for advertising – eg Facebook, Twitter and Instagram; and some eg Google and Amazon track and provide information to resellers if you don’t block them from doing so. As an example of how much value Google sees in getting knowledge of what you’re doing and where you’re doing it, they pay Apple up to $20bn annually to remain as the default search engine for any browser that’s running on an Apple device! Sometimes you may click on a link and have been asked whether you wanted to accept cookies – what exactly are they, and what do they do. This article from Norton explains what they do quite well … Essentially, they record what you do on a website so that when you return to it some of the settings are remembered and applied. Cookies do however also have a downside in that some can also act to track your activity once you’ve left the site. For that reason, you should disable in your browser the ability of third-parties to glean information from a cookie, and also to prevent them tracking your activity once you’ve left the site. You can at anytime, clear the cookies from your browser, and indeed on some internet browsers set them up to delete cookies when you leave (close the window) the site. If you use Firefox as your browser it will alert you the first time you go to a site that it is using a Fingerprinting cookie itself. For instance from the Norton site above …
Essentially, they record what you do on a website so that when you return to it some of the settings are remembered and applied. Cookies do however also have a downside in that some can also act to track your activity once you’ve left the site. For that reason, you should disable in your browser the ability of third-parties to glean information from a cookie, and also to prevent them tracking your activity once you’ve left the site. You can at anytime, clear the cookies from your browser, and indeed on some internet browsers set them up to delete cookies when you leave (close the window) the site. If you use Firefox as your browser it will alert you the first time you go to a site that it is using a Fingerprinting cookie itself. For instance from the Norton site above …
Which brings us to browsers and search engines
Search engines are not created equal! Whilst Google is often thought to be the same as the internet and is often mistaken to be an internet browser itself, it is in fact just one of a range of possible search engines that you can use to look for information on the internet. It uses a platform called Chromium to display the results of its searches to you through a browser called Chrome. However, other browsers – Microsoft’s Edge, Brave and Opera all use the same underlying Chromium technology – the difference being they don’t track what you’re doing “to present the content that most meets your needs” (Google’s philosophy) and in some cases (eg Brave) they can actually prevent tracking of your browsing history. I use Safari – which on Apple is my default browser choice, but otherwise I would use either Brave or Firefox as my internet browser. So what safe and private search engine could you use as an alternative to Google. I use DuckDuckGo …
Should you be frightened?
The take away message I want you to have is Frightened – no; cautious – yes! Online banking is very secure – a recent survey in Which? produced the following scores …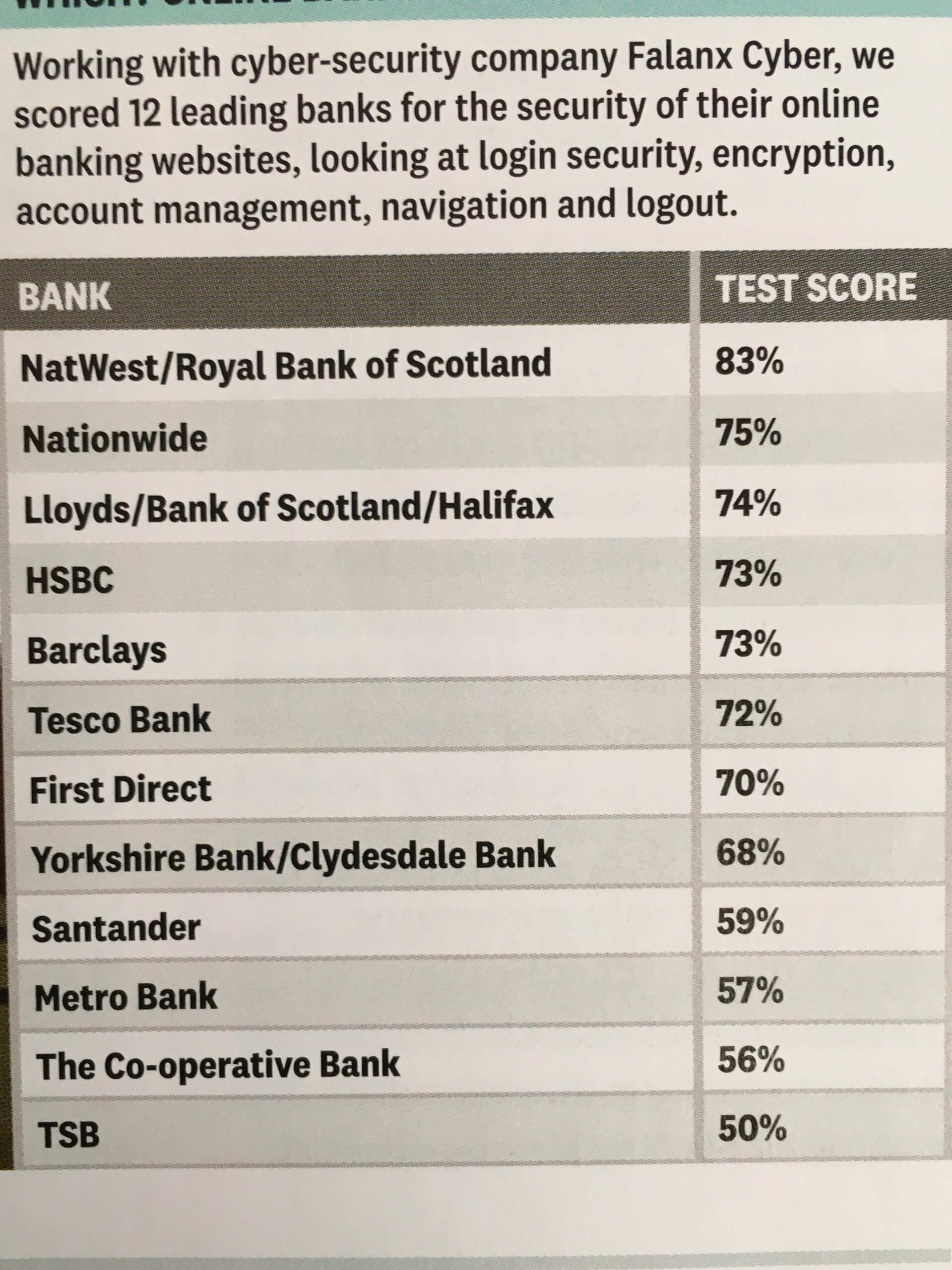
What should you do to protect yourself?
Some of these pieces of advice are really quite straightforward, but some require some intervention by yourselves.- Keep your operating software up to date. This is particularly true if you’re a Windows user, and even more true if you are still running an older version of Windows than Windows 10. If you’re using Windows XP, Windows Vista or even Windows 7 you should seriously consider disconnecting your machine from the internet because even if you’ve got anti-malware software running this is probably not protecting you against the latest threats.
- Install anti-malware, or anti-virus software, particularly if you’re a Windows user. Don’t pay more than you need to. Windows Defender from Microsoft is Free and for our demographic relatively undemanding and unsophisticated users, more than sufficient. Keep it up-to-date as well! [As I said previously, your bank might be offering free software as well.]
- Keep the software you use regularly up to date as well. Consider removing any software from your machine that you don’t use – this is because software vulnerabilities are discovered sometimes quite a while after the software was first released. It will also save you disc space!
- Be cautious over installing extensions into your browser. These are often extremely useful and valuable tools, ie password managers, Dropbox, note taking, Google Back up and Sync, but if you don’t get them from the official sources then you might be importing vulnerabilities, eg spyware and trojans to your system.
- Very seriously consider logging-out from social media and other retail sites when you’ve finished using them, especially Facebook, you just don’t know what tracking and logging of what you do, even where you are, if you leave yourself logged in on a mobile device.
- Free software is both a boon and a curse. Only download open source software from a reputable site such as Softpedia, and never try and get proprietary software for free. Read this article about Free download sites if you want to know more.
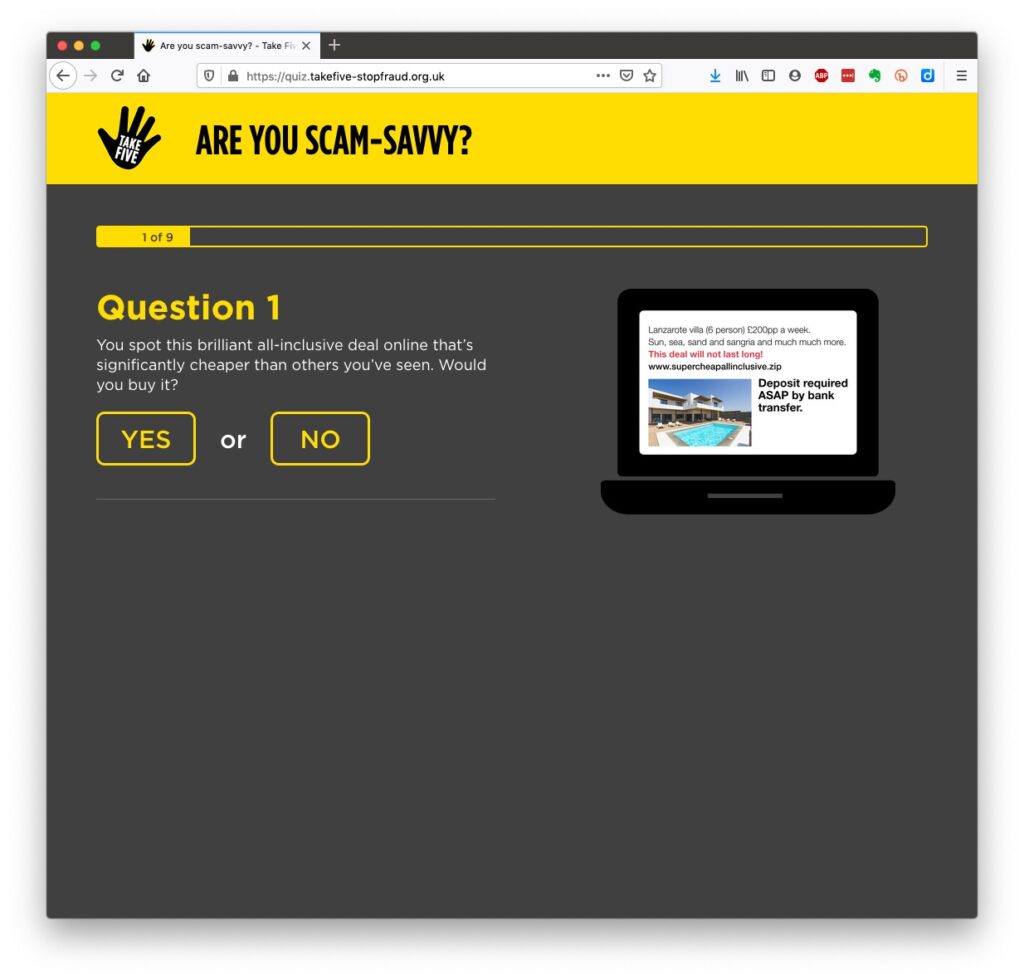
- Remember the golden rule 1 – if it seems too good to be true, it probably is, so steer clear!
- Remember the golden rule 2 – don’t speak to strangers (an oldie but goldie that one); in other words if you don’t know where an email has come from – ignore it; if the website address looks a little strange – do an internet search on the company or organisation to check if the address you’re looking at is a spoof of the proper one.
- Have more than one email address. Use one as your personal address, then use other ones that you can “throw away”when you need to register to a website, but you’re unlikely ever to go back to it again. Or have an email address (UserID) specifically for online purchases. Splitting things like this reduces the risk of you being the victim of fraud.
- Seriously consider using an email service that is NOT connected to your Internet Service Provider (ISP). If you decide to change your ISP, and you should review them periodically, then you will have real problems if your email address is linked to their service!
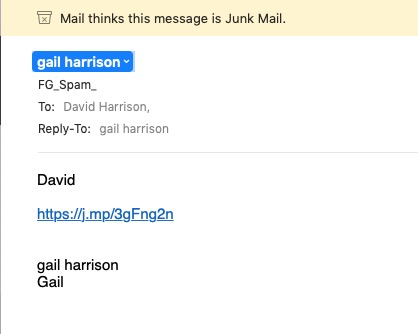
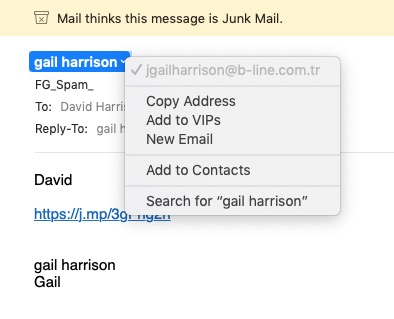
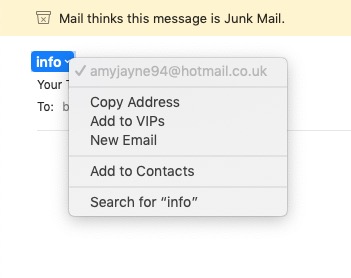
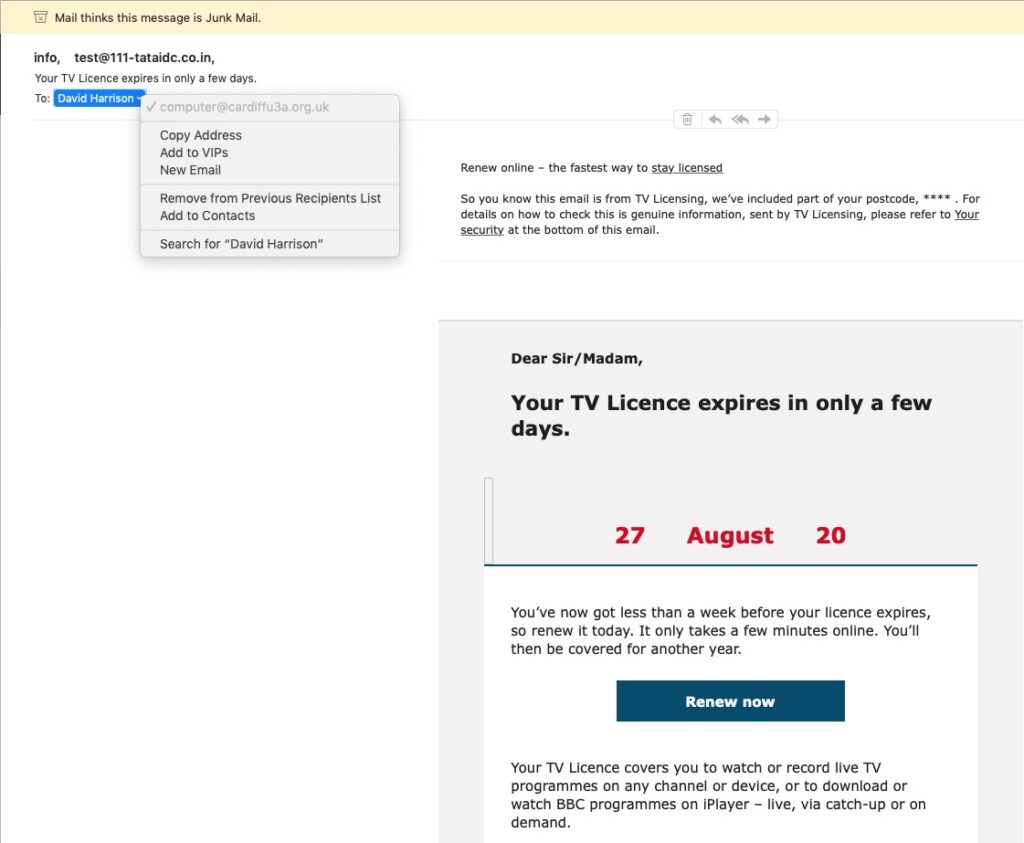
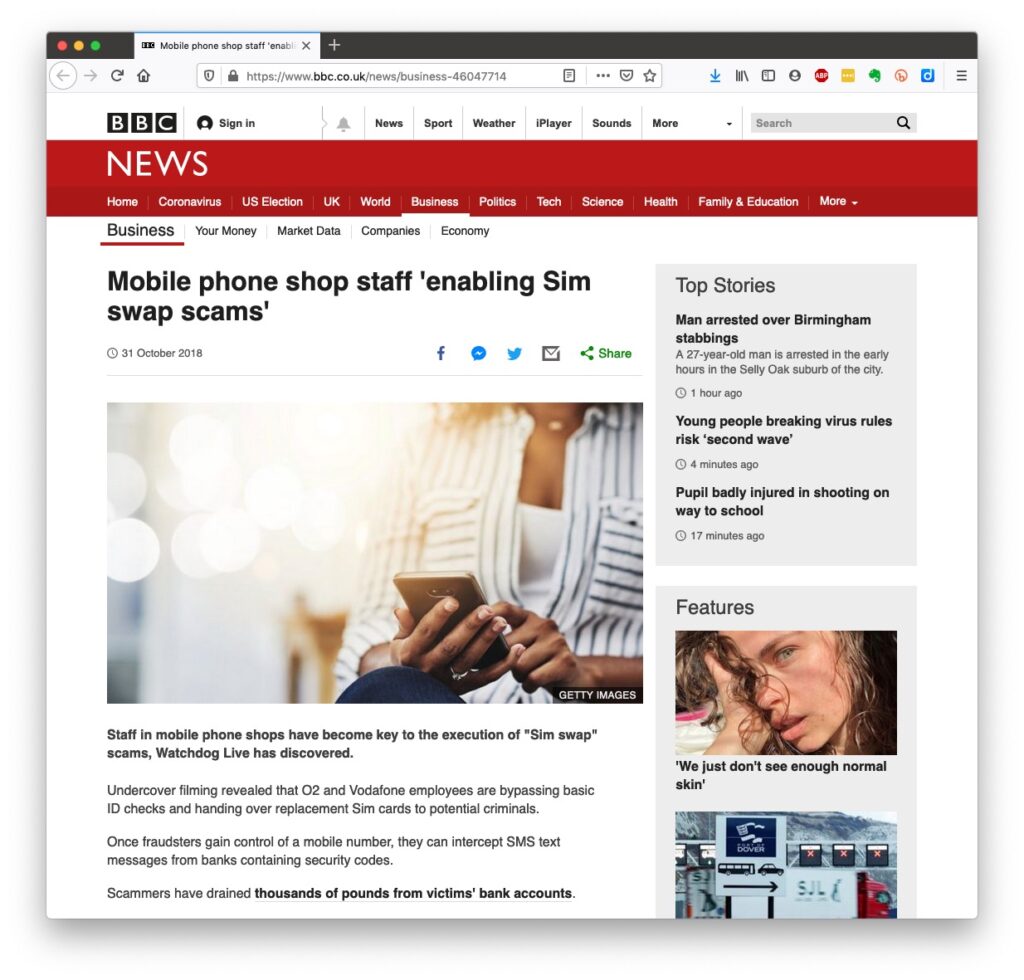
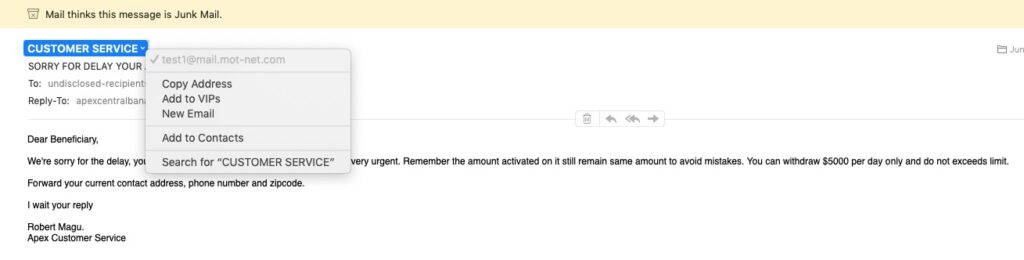
- You’ve got Spam filters running? Of course you have – but you better check! Probably your ISP, or email provider (eg Gmail, Yahoo, Microsoft Outlook or Hotmail) is filtering out what it thinks is spam, but occasionally some gets through. If that’s the case then you can always look at the real sender of your message. Take a look at the examples below …
So we come to Passwords …
… this is the point at which you need to consider intervention and changing your behaviour! You might also need to do a fair bit of work, but it’s worth it if you want to have a secure internet experience. Let’s just see what using an insecure Password can lay yourself open to. Type in the word Password, or ABC123 from the link above – frightening eh!?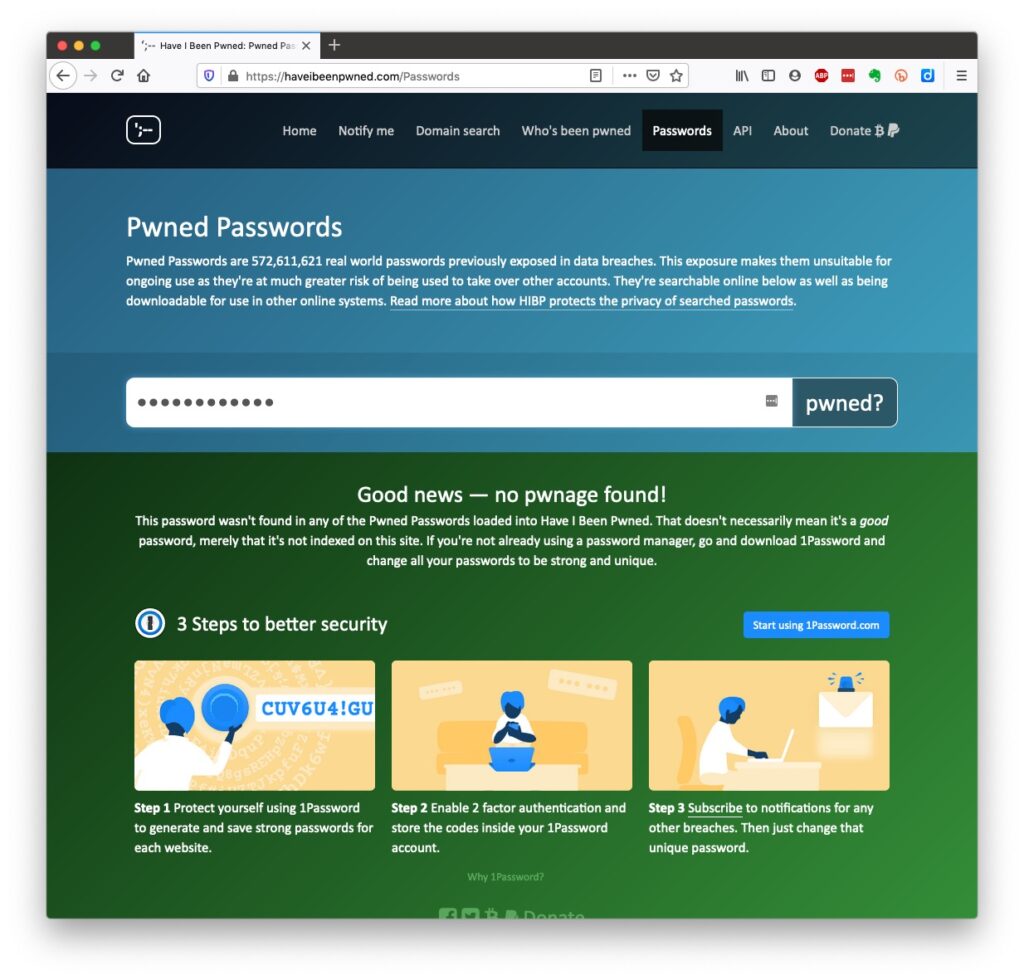
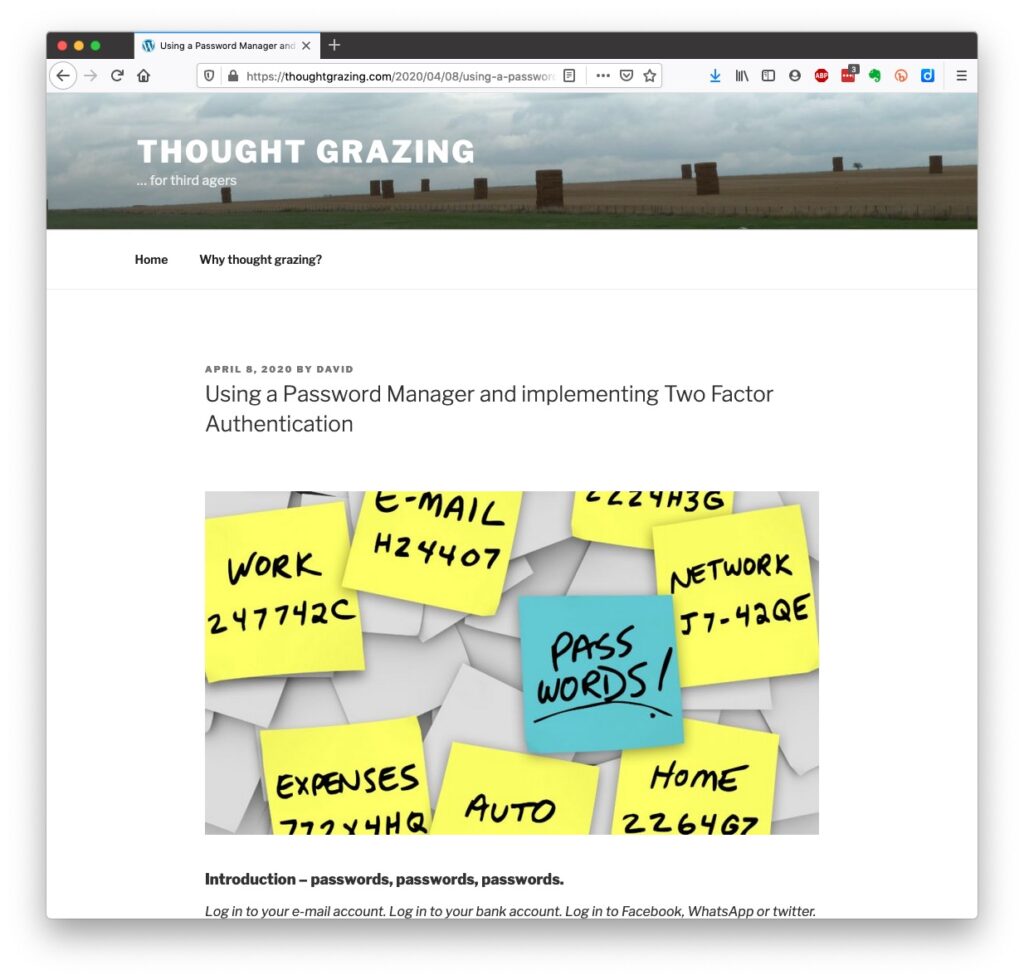
Password managers
I still use LastPass, but as a back-up and archive of my old passwords. I now use Keychain as I only have Apple devices (as do most of my family, and so it makes sense to use a system that is linked to the hardware I use. Other common password managers are Dashlane and 1Password. Please make up your own minds after reading some Reviews and seriously consider using one.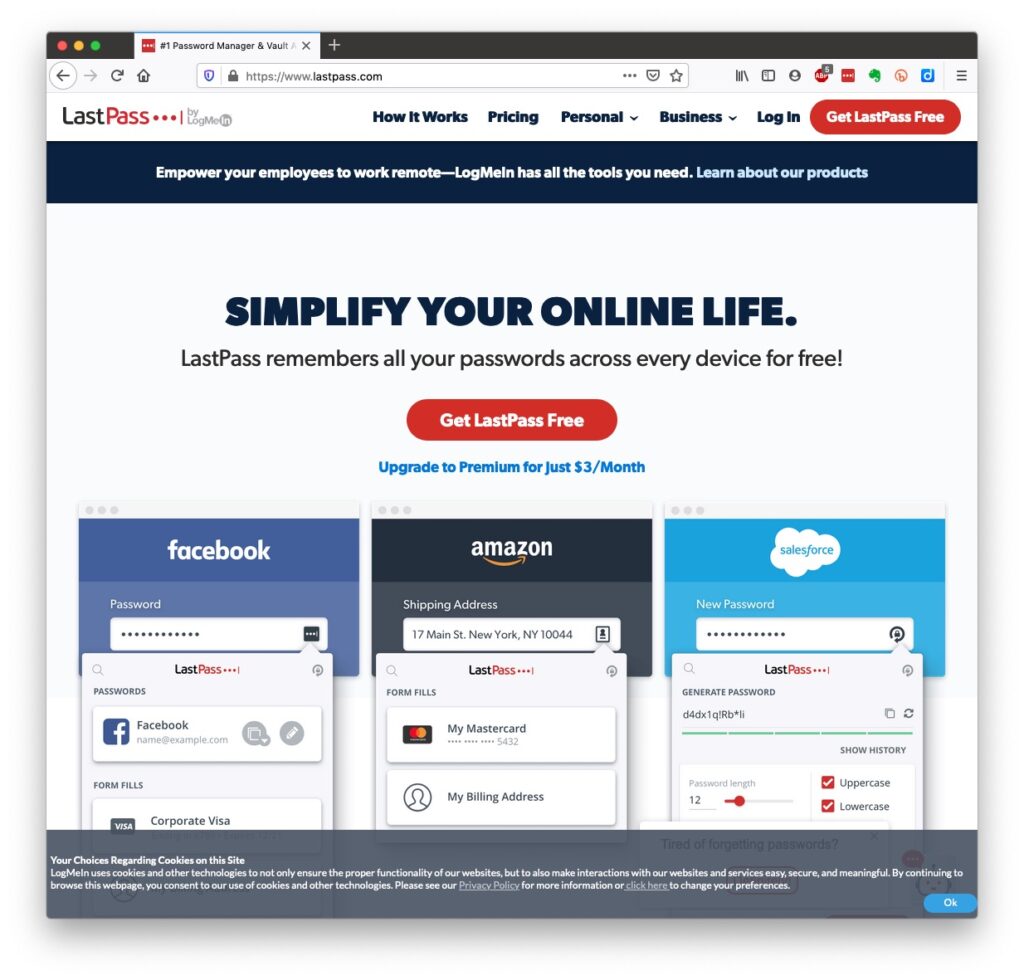
However … the future is Passkeys
The major tech companies – Microsoft, Google and Apple amongst them, have been working in alliance on a project called FIDO that will mean the combination of UserID and Password can be consigned to the waste basket. This article explains what they are, and what it means for us really well. Although Apple stole a lead, announcing their implementation a year ago, Google has now launched it’s implementation, and this article describes how to set them up on your Google account. Microsoft also allow a password-less way forward, but I’m not clear on how to set it up – not being a M$ user. On Apple – here’s how you set up Passkeys on your iPhone, iPad and Mac. Another reason why I chose to move from LastPass to Keychain. Whilst if you’re a 1Password user, you can combine your legacy use of a Password Manager with Passkeys, and these will also work much better together on your iPhone. Watch out for an announcement shortly! [NB It is possible to move between password managers, ie from LastPass to 1Password.] And that’s about it for this year. We can look forward to much more about Passkeys in the coming 12 months; much more about GDPR and how the UK government’s online security legislation is reviewed (and hopefully revised) before implementation; much more about “big tech” and corporations re-acting to whether they are responsible for content, or are just a platform providing a service, rather than a publisher. Interesting times!Slides from talk given to Bridgend U3A
Keeping safe online
Slides from talk given to Cardiff U3A
Staying safe online
References